Thycotic Privilege Manager
About Thycotic Privilege Manager
Mitigate malware and modern security threats from exploiting applications by removing local administrative rights and enforcing least privilege on endpoints
The Data We Collect and How We Use It
The table below lists the fields we collect from Thycotic Privilege Manager and how they map to the fields in our Aurora ASM platform. This data is only used internally; we do not share it with any parties outside of Arctic Wolf Networks. Refer to our privacy policy for details.
Thycotic Privilege Manager Field | Aurora ASM Field |
|---|---|
|
|
|
|
|
|
|
|
Integrate Thycotic Privilege Manager
- Add a source: Follow our instructions to add an Aurora ASM source.
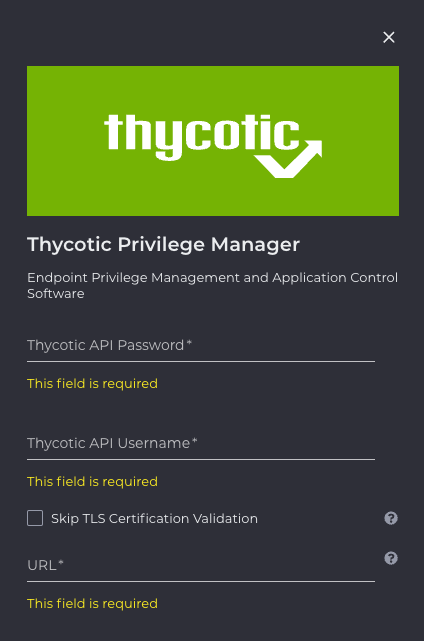
- Provide credentials: You'll be asked to provide source credentials that Aurora ASM will use to connect to Thycotic Privilege Manager:
Credential or Parameter | Description |
|---|---|
| API Key username portion |
| API Key password portion |
|
- Set permissions: In Thycotic Privilege Manager, ensure that user has read access to Agent Installations report
If you encounter any errors, they are most likely related to incorrect credentials or insufficient permissions. Verify your work in steps 2 and 3.
Contact Us
If you're having problems configuring an Integration, or if you've found something wrong in this document, please email us at [email protected].
Updated about 1 month ago